Is Stealth Monitoring Ethical? A Practical & Legal Walkthrough!

Key Takeaways:
-
Stealth monitoring software is ethical only for a clear misconduct case that has a set end date: get approval from HR and legal teams, use only work devices and accounts, collect the least amount of information needed, limit who can see the data, keep it for a short time only, and tell employees about it.
38% of global monitoring tools use stealth mode to track employee performance. But, the concern is whether stealth monitoring is ethical?
Well, let’s find out—
When is Stealth Monitoring Ethical?
When the Device is Monitored, Not the Person
Monitoring using invisible agents is considered only ethical when done using a company-owned device. You should only install monitoring software on devices that your company owns. This means:
- It goes on company-provided computers, laptops, or phones.
- It's active only during official work hours. You wouldn't monitor an employee's personal laptop, nor would you track their activity after they've clocked out for the day. This keeps the focus strictly on work tasks.
Track ethically with transparent monitoring
When You Know What You’re Measuring and Why
Stealth monitoring is only legally allowed and considered ethical when you have a distinct purpose to do so. Without a defined goal or purpose, businesses are not allowed to track their employees.
So, before you even think about monitoring, ask yourself: Why are you doing this? You need to have clear, legitimate business reasons for hidden observation. But it cannot be about general surveillance. Instead, you might use it for:
- Data security: Protecting sensitive company information from leaks or theft.
- Preventing misuse: Ensuring company resources (like internet or software) are used for work, not personal errands.
- Ensuring productivity: Understanding workflow to help teams be more efficient, especially in remote settings. You should be able to clearly state your objective.

Monitoring What’s Necessary—Nothing More
When a business starts invisible tracking, it should only track what is necessary for the business. For instance, if the purpose is monitoring employee productivity, a business should not track an employee’s out-of-work-hour activities.
On the otherhand, if the purpose is to ensure compliance security, employers should not track any data that is not related to security.
However, monitoring should never be done out of curiosity or habit. You should know exactly what data you are collecting and what problem it helps solve. Whether the goal is security, productivity, or compliance, having a clear purpose prevents misuse and keeps monitoring focused and responsible.
Transparency
Well, transparency in undetectable stealth mode monitoring sounds quite confusing. But many experts, like those at Workforce Next, argue that transparency in policy is key, even when the software operates discreetly.
But, how would you monitor secretly, if you have to keep it transparent? Here’s how—
- You should clearly communicate that monitoring may occur in your employee handbook or onboarding documents.
- Explain what kind of data might be collected and why.
- This way, employees are aware of the possibility, even if they don't see the software icon every day. It builds a foundation of informed consent.
When is Stealth Monitoring Unethical?
Invisible tracking of your employees' devices also has limitations. As a company, if you cross that line, this simple thing can turn into an unethical headache.
So, before you start measuring your employee work data, be aware of these unethical steps–
Broad Spying
Monitoring becomes unethical when everything is tracked “just in case.” If you collect data without a clear reason, it creates fear and confusion. People feel watched instead of supported, and trust breaks down fast.
Targeting Individuals
If you use stealth monitoring with a target to quietly monitor any specific employees, it’s something unethical that you must stop. When you single out an employee without any real cause, it can lead you to unfair treatment or even made-up reasons for discipline. Therefore, monitoring should apply to roles or teams, not secret personal watchlists.
Monitoring Personal Devices/Accounts
Even if your intention is good, monitoring can cross ethical boundaries when you start tracking activity on employees’ personal devices. It becomes even more sensitive when personal accounts or private tools are accessed without consent. This kind of monitoring quickly breaks trust. Hidden mode stealth monitoring is ethical only when it focuses on company-owned devices, tools, and accounts.
Punishment Focus
When employers start monitoring to punish employees, it becomes unethical. Monitoring should help people grow without creating fear. Using numbers alone to discipline someone is unfair. It ignores the full situation. This behavior builds distrust at work. Monitoring data should be used for coaching and feedback. It should support development, not constant enforcement.
Implement ethical tracking the right way
How to Do Stealth Employee Monitoring Ethically
Stealth or covert monitoring is ethically fragile. You should treat it as an exceptional and temporary investigation tool, not a default way to measure productivity. If used carelessly, it can quickly damage trust and workplace culture.
So, how do you start employee monitoring without hurting the company morale? Here are a few proven steps highly-managed companies are following with success—
1) Start with the “Eligibility Test”
Before you monitor anyone secretly, ask yourself why you are doing it.
Legitimate Purpose
The strategy to know whether you are monitoring with ethics or not is simple. When you know your purpose starts with a clear and serious reason, this is when it’s considered ethical.
You should always have a legitimate business reason to start monitoring your employees. Acceptable reasons include credible signs of fraud, data theft, harassment, safety risks, or compliance violations.
What does not count as ethical are vague concerns about productivity, gut feelings, micromanagement, or broad attempts to “see what people are doing.”
Exceptional Circumstances + Last Resort
In most cases, a company should let its employees know they are being monitored. However, covert monitoring can only be used when being transparent would prevent you from finding the truth.
So, if there are exceptional circumstances, and no other ways to solve any work-related issues, secret monitoring is considered ethical. If there are other reasonable ways to address the issue, those should come first.
2) Governance & Approvals
As an HR manager or a team lead, you should never take monitoring ethical with your own hands. Instead, it's a decision that should come from multiple individuals, such as seniors.
Senior Authorization + Separation Of Duties
So before you start, get approval from senior leadership and, where possible, HR, legal, and security teams.
Do not provide all the responsibilities under a single individual's control. Instead, separate the duties to different employees so there’s no chance of favoritism and other unwanted incidents. Besides, clearly define who is investigating, who controls the data, and who reviews the findings. This separation helps prevent misuse and bias.
Document the Decision
You should always write these things down because it forces you to slow down and think clearly before you act. When you explain why monitoring is needed and what evidence you already have, it helps you confirm that the decision is fair and not based on assumptions. Writing down why other options will not work shows that monitoring is truly a last step, not a shortcut.
Documenting how long monitoring will last and what data you will collect protects everyone involved. It allows you to avoid collecting more information than necessary and helps you stay focused on the real issue. Recording how the data will be protected also shows that you respect privacy and take responsibility for sensitive information.
3) Privacy-By-Design Setup
Choose the Least Intrusive Monitoring Method
It is always better to start your stealth monitoring journey with the least intrusive options. For instance, starting with security-focused data like access logs or system alerts instead of invasive tracking. You can also avoid collecting webcam, microphone, or personal message content unless there is no other option. It helps you monitor employee performance in quiet mode without breaking their trust.
Narrow the Scope
The scope of stealth employee monitoring should be narrowed down to specific matters. For instance, you should monitor specific devices, systems, or a time period. If you are starting a hidden observation of any specific employees, it must have a hard end date limit.
Choose privacy-first monitoring software
4) Mandatory Risk Assessment + Legal Hygiene
Do a DPIA / Privacy Impact Assessment
Monitoring in secret is almost always high risk because of the power imbalance between employer and employee. Therefore, taking a DPIA helps you identify those specific risks. For instance, you can identify the accidental collection of private data and set up safeguards to fix those.
Check Jurisdiction-Specific Notice Requirements
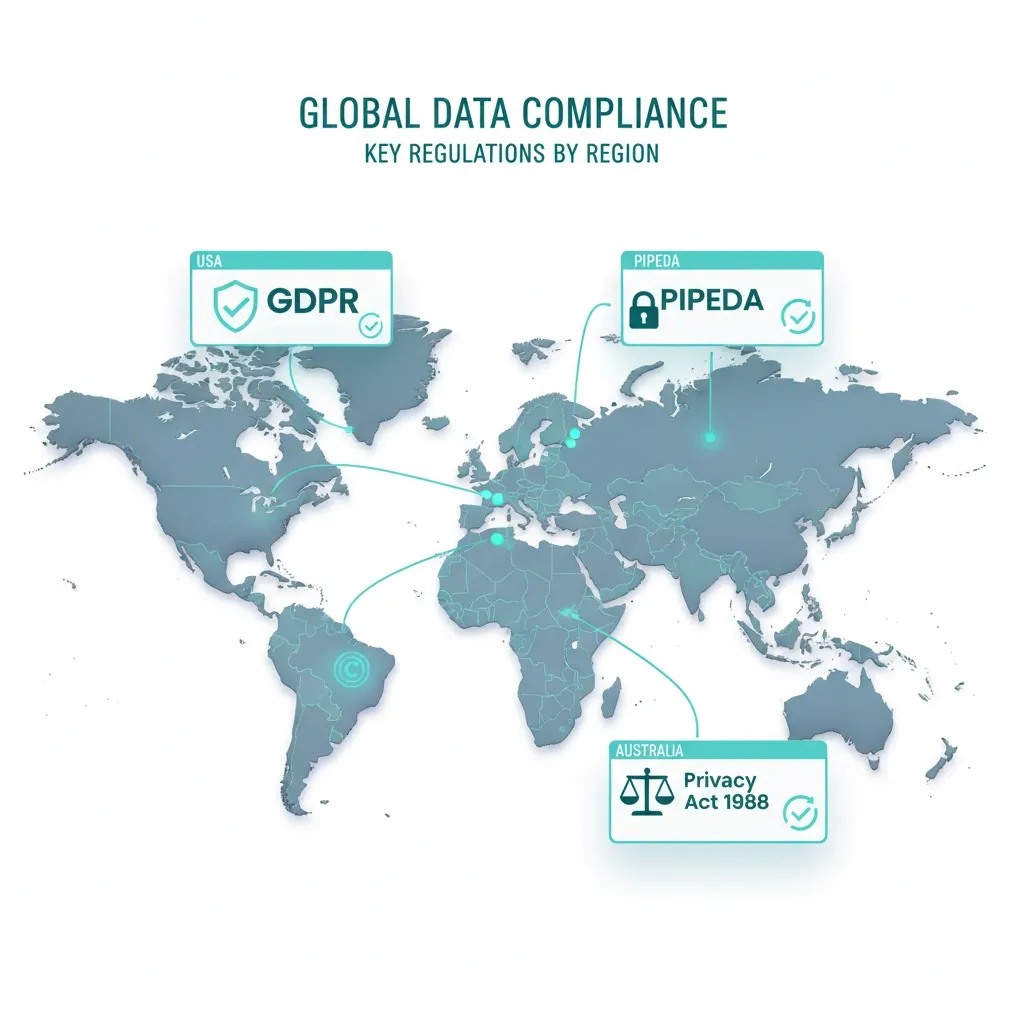
Stealth monitoring is not allowed in every country. Most countries have restrictions on how you are going to track and use the employee data. Therefore, you should also check stealth monitoring laws before starting quiet mode observations.
In some regions, employers must clearly explain monitoring in contracts or handbooks. Certain spaces must never be monitored, and some locations require prior notice even for electronic monitoring. Laws vary, so skipping this step can create serious legal trouble.
5) Safeguards During Monitoring
Data Minimization Rules
To do ethical stealth monitoring, only collect the data that you truly need. You can also minimize the tracking process by tracking specific events. You should also be careful about personal data collection. If it happens accidentally, isolate that information and limit access from the others.
Collect only necessary data automatically
Security Controls
You should also be careful about access to the data. It should not be accessed without the authorization of the people across the organization. Even, you should ensure all the accesses are logged, and the data are also stored securely. When the data are no longer necessary, they should be deleted immediately so these short retentions can prevent misuse of confidential data.
6) Fair Process And Post-Investigation Steps
Avoid “Automation Bias” and Unfair Scoring
You should not take your collected data as a source of productivity measurement. The numbers your monitoring software provides can be misleading if there’s no viable context.
Post-Investigation Transparency and Close-out
Now, you may not always conduct a meeting and explain to everyone why you are starting stealth monitoring. But you can always inform your team afterward once it’s safe and allowed by law. When the investigation ends, you can stop monitoring immediately. In that case, always remove unnecessary data, document the outcome, and use the experience to improve policies and training.
7) Red Flags
Stealth monitoring can turn out to be the biggest nightmare for the unethical use as well. Watch out for these warning signs that monitoring has gone too far:
- Total Surveillance: Tracking every single keystroke or taking constant screenshots often captures private passwords.
- Off-Hours Tracking: Monitoring after work hours is a major invasion of your employees' personal lives.
- No "Paper Trail": If you haven't done a DPIA (Privacy Assessment) or documented your purpose, the monitoring is likely unethical.
- No Oversight: One person should not have the power to watch everyone without a "manager over the manager" checking the logs for abuse.
Conclusion
Stealth monitoring is ethical as long as you follow the laws, rules, and privacy standards of your region.
It should never be about "spying" on people out of suspicion. Instead, you should use it as a professional tool to protect your company and support your team’s growth. By staying transparent about your policies and focusing only on work-related data, you can keep your business secure while still maintaining a culture of trust.
Get started with ethical stealth monitoring today
Frequently Asked Questions
Is stealth monitoring legal in the workplace?
In the U.S., it is usually legal on company-owned devices for business reasons. However, in the UK and EU, the law is much stricter. In those regions, you almost always have to tell employees they are being monitored.
Is it ethical to spy on employees?
The answer varies depending on the purpose. Rather than ‘spying’, if employers use monitoring as a tool for safety or productivity, it is considered more ethical. However, it should not be used just to watch people without a good reason.
How can companies implement ethical stealth monitoring practices?
Firstly, companies must establish a clear policy book in the employee handbook before implementing ethical stealth monitoring. Then, they must ensure no personal information is being tracked. The work-related data should be collected to achieve positive business goals like improving performance. Finally, companies should ensure those data is only accessible by specific authorities and is secure and private.
What are the risks of unethical stealth monitoring for employee trust?
If employees feel "spied on," they stop trusting their organization. This leads to high stress and lower employee morale. People may even start "gaming the system" by pretending to be busy instead of doing real work.
How do employees typically respond when they discover stealth monitoring?
Most employees feel angry or betrayed if they find out they are being tracked in secret. This may often lead to them resigning from the job. It can also cause a "toxic" work environment where everyone feels suspicious of each other.
Is it ethical to monitor employees without telling them?
Generally, no. Most ethical guidelines say that transparency is the best policy. Even if you use "stealth" software, you should include a note in the employee handbook that monitoring may occur. This respects the employee's right to know.
Can employers secretly monitor computers/laptops?
Technically, software allows it. However, doing it in secret is risky. If you don't have a strong legal reason, like a criminal investigation, it can lead to lawsuits and unhappy employees.
Is keylogging ethical at work?
Yes, but only under strict conditions. It should only be practiced on company-owned devices. If the purpose is only for business reasons and security compliance, the questions about ethicalness are not raised. But when keylogging captures personal information secretly, it is considered unethical.
Are screenshots of employees ethical/legal?
If a company captures screenshots for business or security purposes, it is legal and ethical. However, taking screenshots of an employee’s private information without their consent is illegal and can destroy company morale.
Can my employer read my emails?
Yes, your employer can read your work emails if you are using company-provided email ids. However, your company has no right to read or track the emails of your personal email address.
Do employers need a DPIA / privacy impact assessment?
In many regions, yes. If monitoring could affect employee privacy in a significant way, a DPIA helps employers understand risks, follow the law, and show that monitoring is necessary and proportionate.
What should an employee monitoring policy include?
It should clearly explain what is monitored, why it is monitored, when monitoring happens, and how the data is used and protected. It should also state who can access the data and how long it is kept.
What can employees do if they think they’re being monitored unfairly?
Employees can ask for clarification from HR or management and request to see the monitoring policy. If concerns remain, they can raise a formal complaint or contact a labor authority or data protection body, depending on local laws.
